With the continued increase of applications hosted in the cloud, companies, schools and colleges have struggled with providing simple and secure access to their employees, students and faculty. This includes from within the organization’s network on company-owned computers as well as from a plethora of device types including laptops, tablets and smartphones employees and students use to log in from home or on the go.
Web SSO (single sign-on) holds the biggest promise for helping all types of organizations simplify user access and increase security, while allowing users to log in from any device, anywhere and at any time.
The concept is really quite simple and elegant. A Web portal is created that contains icons or shortcuts to all of the organization’s authorized Web applications. Users log into this portal with their standard network credentials and are easily and securely validated for all of these applications. The portal is dynamic insofar as it will only display applications that a user is authorized to utilize. Web SSO solutions are relative newcomers and provide the greatest benefit for an organization where the majority of applications are cloud based and the users access data from personal devices.
One of the downsides to Web SSO, however, is that it is typically limited in functionality, since it only works with cloud-based applications and those that comply with one of the industry standards, such as SAML, OAuth or OpenID. Communicating with legacy apps, or those that have not adopted one of these standards, requires a more traditional or enterprise-level solution.
For these situations, an enterprise SSO would generally be utilized. Enterprise SSO products typically require a plugin to authenticate back to a directory service, such as Active Directory, to capture the credentials of a user in a secure database rather than using an identity provider. These types of solutions have been available for many years and are widely implemented in locations where the vast majority of users access on-premises applications from a computer attached to the company network.
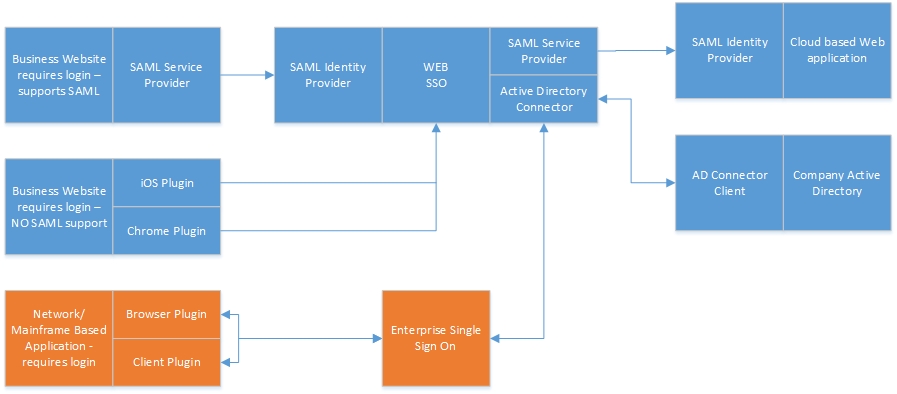
Obviously the best approach for many organizations is a hybrid model. Any apps that are cloud-based or standards compliant should make use of the Web portal; when apps cannot be accessed via these methods, a client-based solution should be available to provide a more complete SSO solution for end users.
The following diagram shows how a hybrid model can communicate with all types of applications from all different devices:
© 2015. Tools4ever
One of the benefits of the hybrid model is that end users can have access to cloud-based apps from anywhere, be it at home, an airport or from a hotel. The network-based apps can also be available via a VPN connection to the network, again from anywhere. This provides a complete SSO option regardless of the type of application utilized.
To increase security even further, many companies are implementing a two-factor authentication (2FA) protocol – something you know and something you have. For years, the U.S. government has provided smart cards and readers to employees who need to access secure information from a personal computer. Smart cards, when coupled with a secure password or PIN, significantly decrease the risk of unauthorized access. The 2FA technologies are extending into more common usage, such as one-time-use PIN codes delivered via SMS or the adoption of near-field communication on smartphones.
In short, before rushing out to get an SSO application, perform a proper evaluation of your organization’s requirements. Determine the predominant types of users – where and how they access applications and type of applications they access. Your organization can then decide if the implementation of Web SSO, enterprise SSO or a hybrid of both is needed to provide a complete solution for your users.
Dean Wiech is managing director of Tools4ever, a global provider of identity and access management solutions.
